BYOD介绍
什么是BYOD? What is BYOD?
Bring Your Own Device (BYOD) refers to the policy of permitting employees to bring personally owned devices (smart phones and tablets) to their workplace, and to use those devices to access privileged company information and applications.
BYOD provide a comprehensive and intuitive set of self-service tools that allow users to complete basic tasks like enrolling, and wiping data from lost devices. Transfer these and other common mobile device management tasks to users so IT can focus on more strategic goals, such as expanding the corporate BYOD program and minimizing BYOD security risks.
Allow users to self-register devices and quickly get secure access to email and business apps.
Offer a self-service portal where users can lock, unlock, view compliance, and retire devices.
Maintain an enterprise app store to give employees a single repository to install, and upgrade business apps.
为什么要使用BYOD? Why BYOD?
Mobile security, or more specifically mobile device security, has become increasingly important in mobile computing. Of particular concern is the security of personal and business information now stored on smartphones.
More and more users and businesses use smartphones to communicate, but also to plan and organize their users' work and also private life. Within companies, these technologies are causing profound changes in the organization of information systems and therefore they have become the source of new risks. Indeed, smartphones collect and compile an increasing amount of sensitive information to which access must be controlled to protect the privacy of the user and the intellectual property of the company.
Security countermeasures are being developed and applied to smartphones, from security in different layers of software to the dissemination of information to end users. There are good practices to be observed at all levels, from design to use, through the development of operating systems, software layers, and downloadable apps.
Secure Any Device
Configure and apply consistent data security policies across Android, iOS, macOS and Windows 10 mobile devices and desktops, with Mobile Device Management (MDM) capabilities.
Secure Email
Provide secure access to business email, calendars, and contacts while preserving the native mobile user experience.
Secure Apps
Protect business data at rest and in motion with industry leading mobile application management (MAM) capabilities.
Secure Mobile Content
Mobile content management (MCM) capabilities allow secure, instant access to content repositories like SharePoint on mobile devices.
Secure BYOD
Maintain user privacy while applying corporate policies and preserving control over business data on personal mobile devices and desktops, whether Android, iOS, macOS or Windows 10.
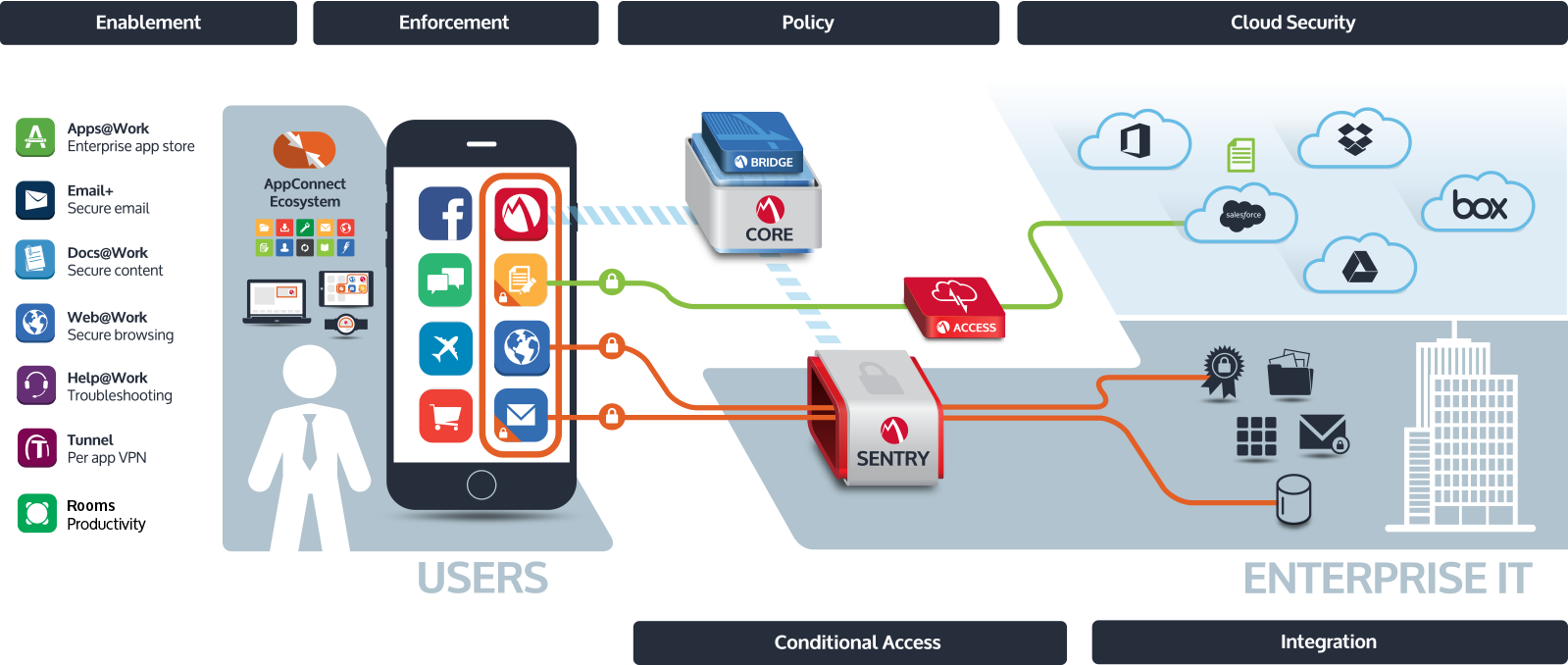
BYOD平台架构 BYOD Platform Architecture
怎么使用BYOD? How to use BYOD?
BYOD申请
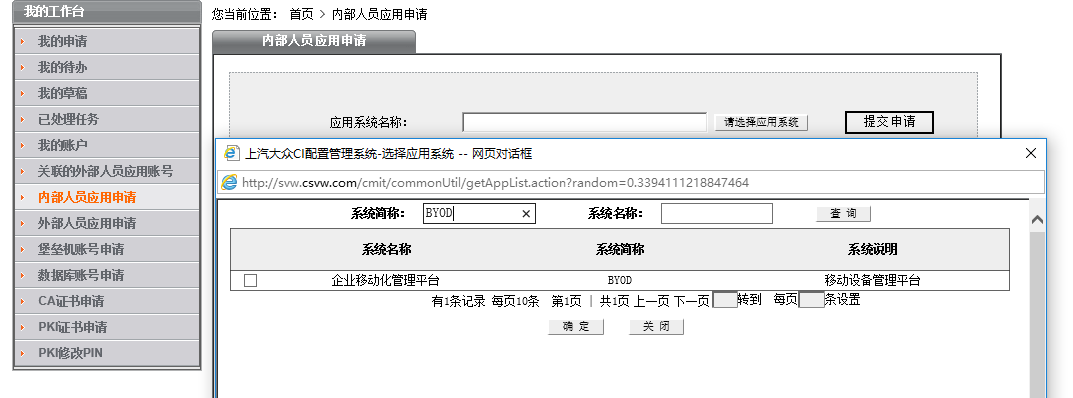
Q-N-1:BYOD平台支持每个用户注册多少台设备?如何注销不用的旧设备?
- 考虑到License的费用支出,我们支持每个员工同时注册2台设备,如有第三台设备需要注册,可以通过BYOD自助服务平台停用不活跃的设备后再注册新设备(停用设备会将设备上的公司数据如邮件、公司应用等从设备上移除)
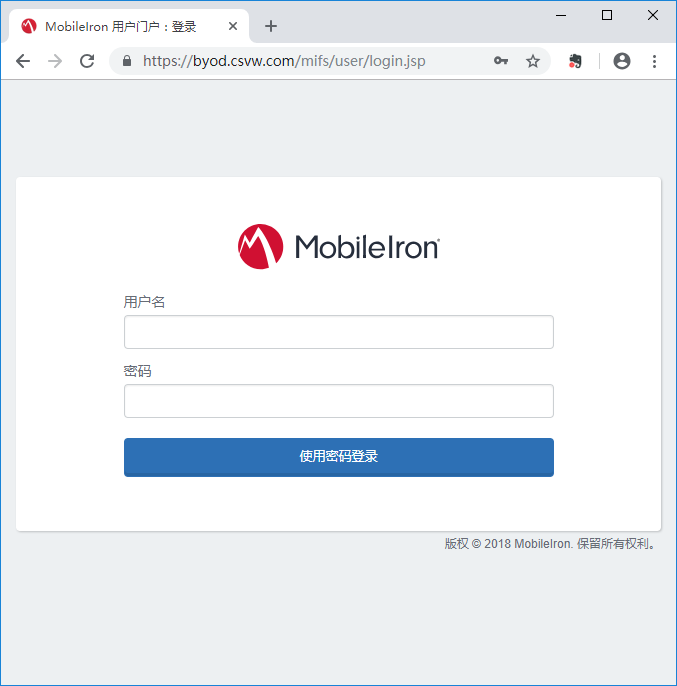
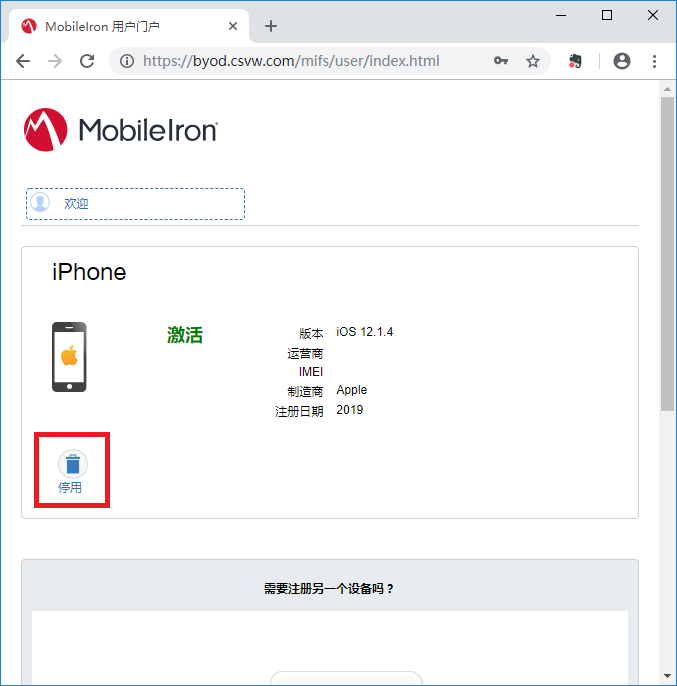
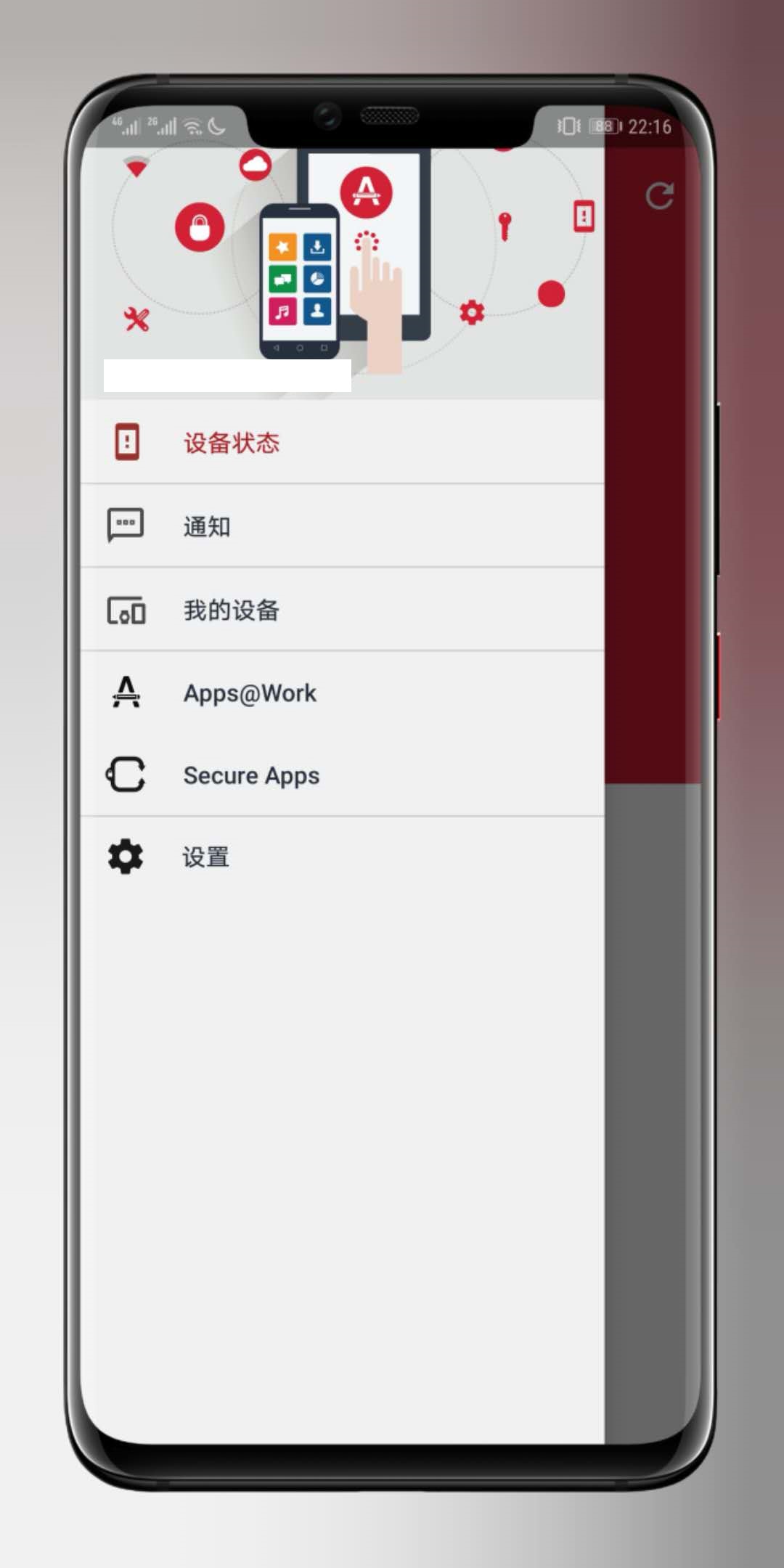
- 或者在MobileIron App客户端的“我的设备”中注销旧设备

BYOD设备注册和使用
苹果iOS平台BYOD用户手册
谷歌Android平台BYOD用户手册
微软Windows 10 Mobile平台BYOD用户手册
点击此处查看微软Windows 10 Mobile平台BYOD用户手册
第三方APP开发和集成
- 文档完善中